
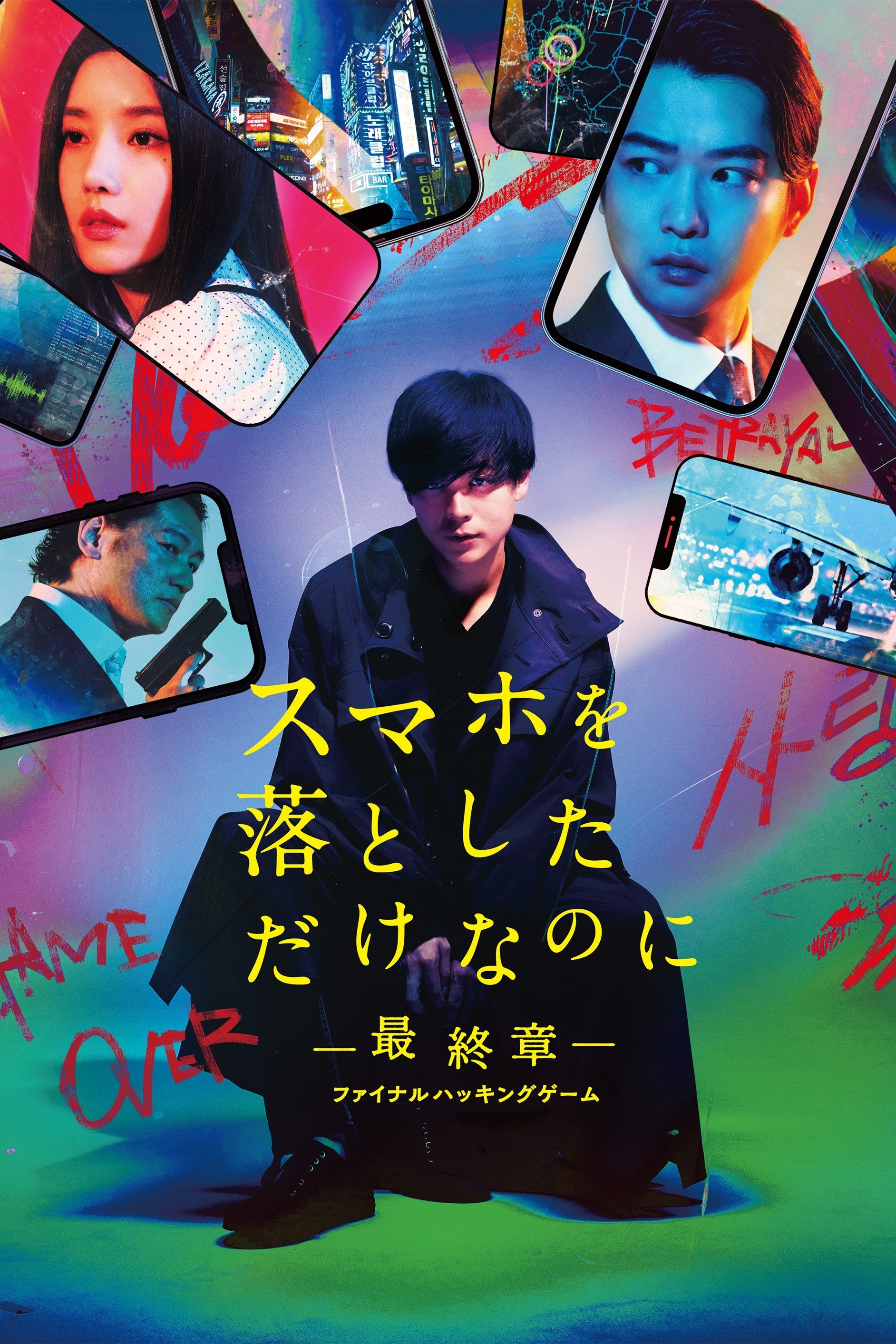
Movie spotlight
Stolen Identity: The Last Hacker
Genius hacker and murderer Urano escaped from prison and fled to South Korea. Urano was hired by a South Korean anti-government organization to set a trap targeted for the Korea-Japan summit meeting. Sumin is assigned to watch over Urano but is intimidated by his frantic behavior. Urano distrusts her, but gradually their feelings begin to change a little.
Insights
Plot Summary
In a near-future world where digital footprints are paramount, a legendary hacker known only as 'The Ghost' is framed for a massive cyber-theft that threatens global financial stability. Pursued by relentless federal agents and shadowy corporate interests, The Ghost must race against time to clear their name and expose the real culprits before their own identity is permanently erased from existence.
Critical Reception
Early reactions to 'Stolen Identity: The Last Hacker' suggest a fast-paced, visually slick thriller that capitalizes on contemporary anxieties about technology and privacy. Critics have noted its intricate plot twists and strong central performance, though some have pointed to occasional reliance on familiar genre tropes. Audience buzz has been generally positive, highlighting the film's engaging action sequences and suspenseful narrative.
What Reviewers Say
Praised for its gripping suspense and timely themes.
The film's visual style and intricate plot were frequently lauded.
Some critics found the narrative pacing uneven in parts, but overall engaging.
Google audience: Google users have largely responded positively to 'Stolen Identity: The Last Hacker', appreciating its exciting plot and the lead actor's portrayal of a morally ambiguous hacker. Many found the film's exploration of digital security and identity theft to be thought-provoking and relevant. A common point of praise is the film's ability to maintain tension throughout its runtime, making for an enjoyable viewing experience.
Awards & Accolades
Nominated for 'Best Editing' at the 2025 Tech & Cinema Awards.
Fun Fact
The distinctive sound design for 'The Ghost's' hacking sequences was created using modified recordings of everyday office equipment, such as dot-matrix printers and old dial-up modems.
AI-generated overview · Verify ratings on official sources