
TV Show spotlight
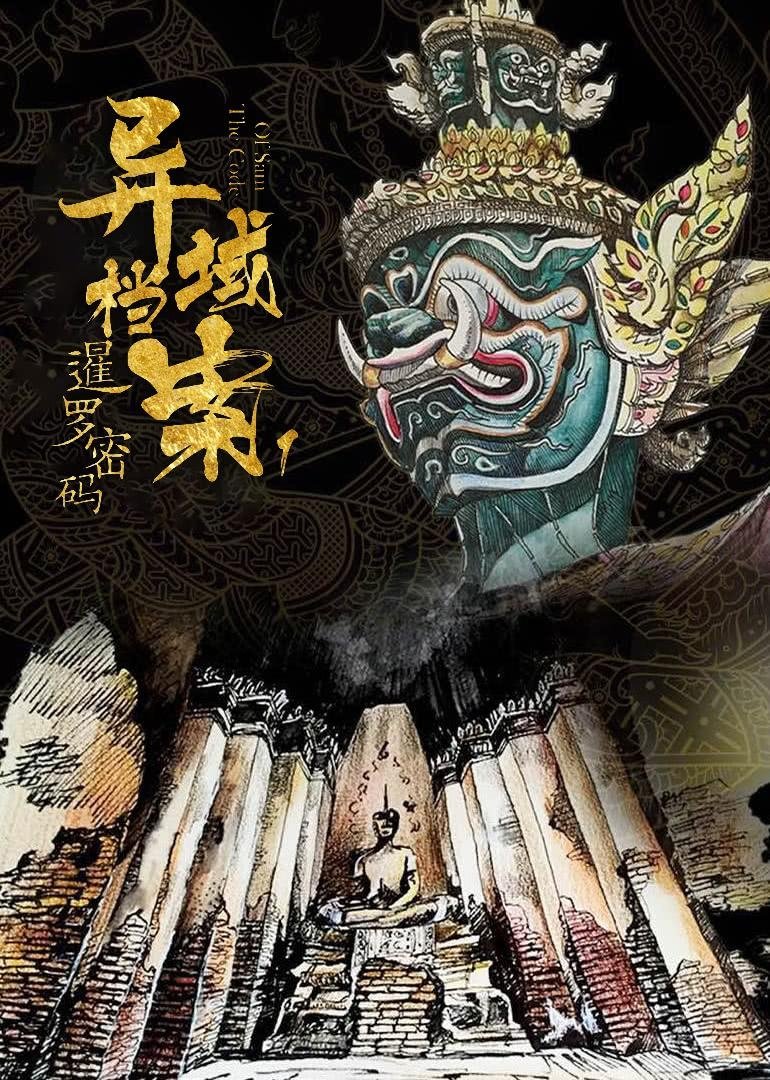
The Code of Siam
A man walking the thin line between good and evil is an ingenious criminal. Yet he abides by the law and serves time in prison. One day before release, his ex-girlfriend who also happens to be his biggest rival runs into serious trouble, leaving him no choice but to escape in order to save her. The story originates in the Golden Triangle where drug trade is proliferate. Xia Tian gambles with his life against a notorious drug lord and wins big. News of Xia Tian's misdeeds reach Zhang Li who works for the Interpol. As it turns out, she is Xia Tian's ex-girlfriend and the apple of his eye. Despite being cop and bandit, the two were lovers who relished engaging in a game of cat and mouse.
Insights
Plot Summary
A skilled hacker, burdened by a dark past, is drawn into a dangerous world of corporate espionage when he uncovers a conspiracy involving a powerful tech mogul. To protect his loved ones and expose the truth, he must use his digital prowess to navigate a labyrinth of cyber threats and betrayals. The film explores themes of redemption and the corrupting influence of power in the digital age.
Critical Reception
While "The Code of Siam" received mixed reviews, it was generally praised for its stylish direction and engaging action sequences. Some critics found the plot to be convoluted at times, but the performances, particularly from the lead, were often highlighted as a strong point. The film resonated with audiences interested in tech thrillers and fast-paced narratives.
What Reviewers Say
Praised for its slick visuals and modern aesthetic.
Engaging action sequences and a compelling lead performance.
Some found the plot to be a bit predictable or overly complicated.
Google audience: Audience reviews for "The Code of Siam" often point to its visually appealing presentation and exciting action as highlights. Some viewers felt the story could have been more original, while others were satisfied with the thriller elements and the hacker protagonist's journey.
Fun Fact
The film reportedly utilized actual cybersecurity professionals as consultants to ensure the authenticity of the hacking sequences depicted.
AI-generated overview · Verify ratings on official sources